Since 2002 the Information Security Group Smart Card Centre has been conducting pioneering research in the fields of smart cards tokens security and applications. This has resulted in more than 200 papers in international conferences and journals and two books published by Springer.
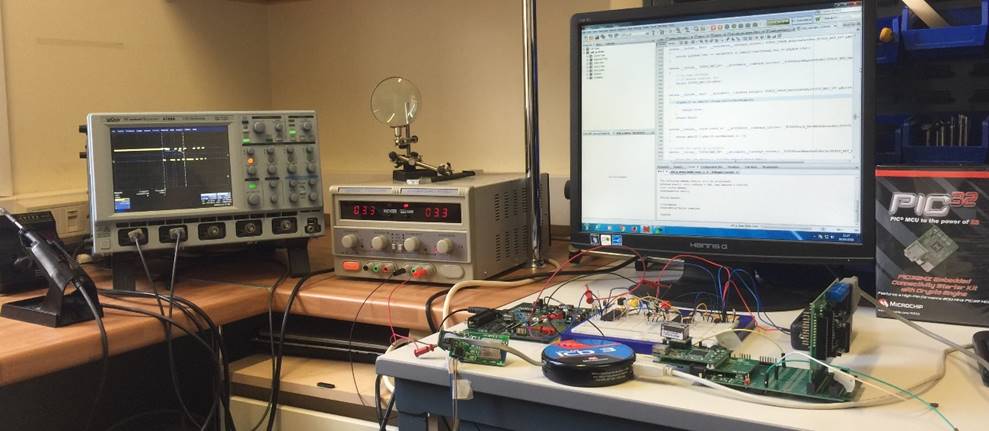
However, the SCC is naturally involved in number of research areas touching the boundaries of embedded systems, mobile devices and Internet of Things (IoTs). A snapshot of our research activities can be obtain from our list of publications but also from the following list.